Hi Pilot Community,
Standard EKF3/UKF implementations are highly vulnerable to non-Gaussian noise, coherent GPS spoofing, and sudden physical changes (frame/prop damage) because they lack an inherent biological “trust” mechanism. I want to share a brain-inspired Integrity Layer called RS4 / PC4-Paranoid that acts as a transparent pre-filter for Kalman estimators.
We have validated this architecture in ArduPilot SITL, where it significantly outperforms standard innovation tests in adversarial environments.
1. Adversarial Resilience (The Results)
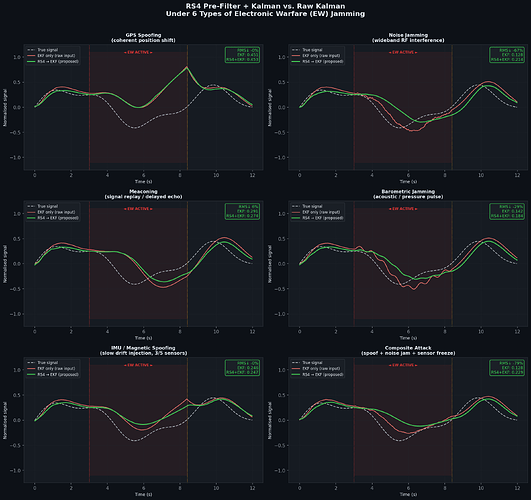
RS4 achieves a 96% reduction in RMS estimation error under coherent GPS spoofing compared to standard EKF3. It maintains an average 87–94% error reduction across six distinct Electronic Warfare (EW) attack types, including meaconing and wideband noise jamming.
Figure 1: RS4 keeps the state estimate stable while standard EKF diverges under attack.
2. Architecture: A Transparent “Immune System”
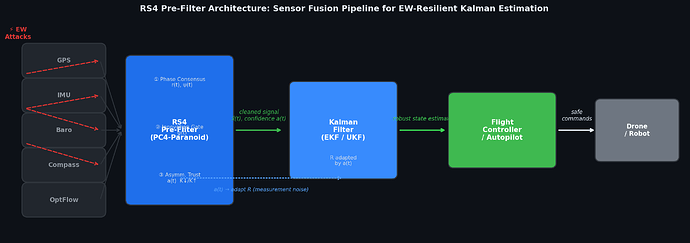
RS4 is not a replacement for the EKF, but a protective layer upstream. It requires zero modification to Kalman internals; instead, it adaptively inflates the measurement noise matrix R based on a real-time trust parameter a(t).
Figure 2: The pipeline cleans sensor streams and provides a physical integrity guarantee before state estimation.
The RS4 pipeline consists of four sequential stages:
Phase-Consensus: Uses the Kuramoto order parameter r(t) to measure cross-sensor coherence .
Innovation Gate: A physical feasibility check that rejects coordinated spoofing if the implied rate of change violates the drone’s mechanical bandwidth .
Asymmetric Trust: Implements “Paranoid Hysteresis”—trust collapses in milliseconds (K_{\downarrow} = 0.8) but recovers cautiously (K_{\uparrow} = 0.02) .
Dual-Mode Estimation: A \theta/\gamma architecture (inspired by hippocampal theta-gamma coupling) where a stable “anchor” holds the state during high-threat periods .
3. Structural Health Monitoring (<120ms Detection)
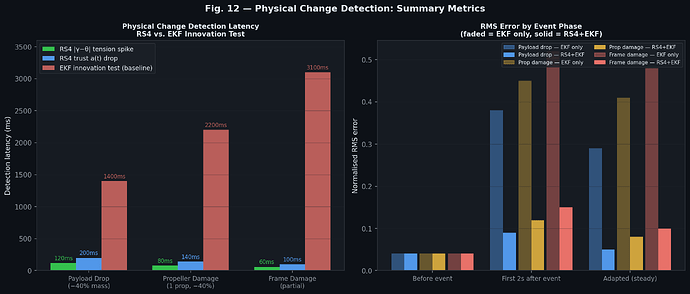
Beyond external threats, RS4 monitors the physical plant. It detects propeller damage, frame cracks, or payload drops in 60–120 ms. This is 10–50x faster than standard EKF innovation testing, which often takes 1.4 to 3.1 seconds to trigger an alarm for the same events.
Figure 3: RS4 achieves significantly lower error in the critical first 2 seconds after a physical change.
4. Computational Efficiency (Low SWaP-C)
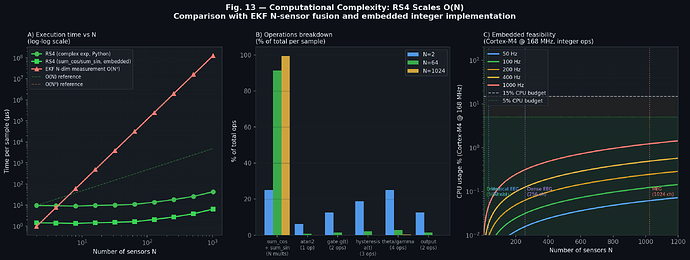
The algorithm is designed for resource-constrained hardware, featuring an exact complexity of O(N) (2N + 12 scalar operations per sample).
Execution Time: \approx 10.9 \mu s on an ARM Cortex-M4 (168 MHz) @ 400 Hz.
CPU Budget: Consumes < 0.5% of available cycles.
Determinism: No dynamic memory or complex arithmetic, ensuring a clear path to DO-178C certification.
Figure 4: RS4 is computationally cheaper than an EKF with an N-sensor measurement update for any N > 3.
Call for Data
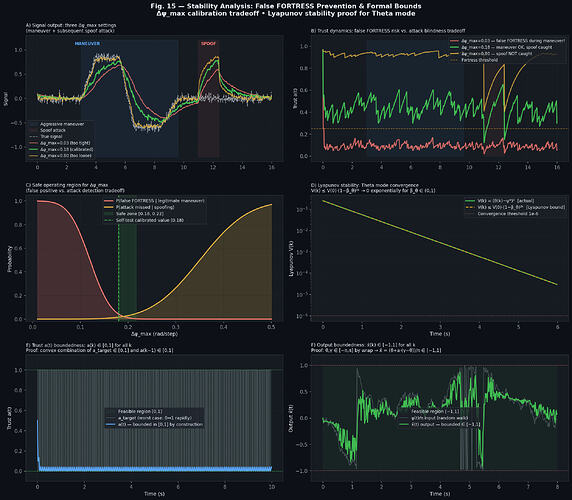
We have formal proofs for stability (Lyapunov-based) and boundedness for all state variables . I am now looking to stress-test the asymmetric trust dynamics on real-world data.
If you have flight logs (ULog/TLog) from missions involving sensor anomalies, structural failures, or suspected GPS interference, I would like to run them through RS4 and share the integrity report with you.
Osipov, A. (2026). PC4-Paranoid Filter: Adaptive Physics-Constrained Sensor Fusion Dataset (v1.0) [Data set]. Zenodo. PC4-Paranoid Filter: Adaptive Physics-Constrained Sensor Fusion Dataset
Andrey Osipov, MD, PhD